Continuous Synchronization
Vulnerabilities in your software may be identified at any time, from initial development phases through to its lifecycle in your production systems. Whether these are security flaws that make headlines, or a simple deprecation of some open source component that you are using (either directly or through one of your dependencies), they can have serious consequences for your business. Developer builds may start failing, your CI/CD pipeline may break, or you may realize that sensitive information in your production systems is exposed.
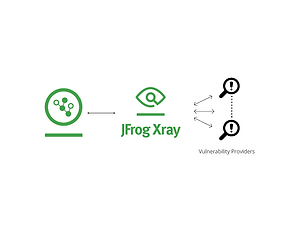
One of the outcomes of JFrog Xray’s deep recursive scanning is a map matching the components and dependencies of your software to the databases and live feeds to which Xray is connected. The continuous synchronization and analysis of live feeds being matched up with your components means that any change in a component, or a new report of a vulnerability or other issue can generate an immediate alert to the right authority within your company regarding the suspicious component. Whether the alert is issued as an indication on a dashboard or an email to the right person, or a notification in your internal messaging system, this virtually immediate response lets you manage the issue with the minimal impact possible.