Download Blocking
Discovering that a component you are using in your production systems has a known security vulnerability can put your whole organization on red alert. Finding all the places it’s used (whether directly or as a dependency), removing it, finding an alternative and refactoring your code is a process that can take your development teams days or even weeks of work. To avoid these scenarios, you can connect Artifactory to JFrog Xray and scan all artifacts that are downloaded to your repositories. As soon as an artifact enters your system, Xray is triggered to run a scan, and can notify your ITSec or DevSec staff about it.
They can then notify your development teams that the artifact is banned, and the development managers can remove it from your repositories. But all that manual handling is tedious, arduous and error prone. Managing potentially harmful artifacts automatically is a much better way to prevent infection of your production systems. Artifactory’s Download Blocking feature does just that.
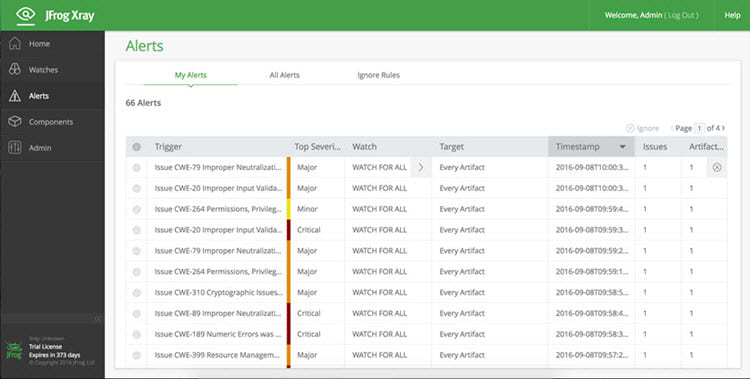
Download Blocking protects you at two levels. First, you can make sure that artifacts are not available for download until they have been indexed and scanned by Xray. The second level of protection gives you finer control over what may or may not be downloaded. Vulnerabilities are graded with a severity level: minor, major or critical. You may want to allow development to continue with minor vulnerabilities while you investigate them further, however, you will certainly want to block artifacts with critical vulnerabilities.

So you can control when to block downloads according to their severity, and receive alerts for any artifact that is blocked. And to make sure your developers don’t get confused when an artifact is blocked, Artifactory displays a notification in its UI, or returns a specific error message for REST API.
With download blocking, your systems are protected against vulnerabilities so you can trust them to perform at their best and do what they’re supposed to do. And, once configured, it all happens automatically and in the background without any manual intervention.



